smart card based authentication via internet Using a smart card in conjunction with a password can add an extra layer of security to protect sensitive patient or customer data. An additional layer of security can be provided here by AI, both through scanning for compromised devices as well as performing risk-based authentication. An NFC reader on a laptop would essentially allow you to do the same stuff as you would with a phone using NFC technology, though would obviously be a lot more inconvenient when it comes to say paying for .NFC readers are the active components in NFC transactions. They can read and write cards .
0 · what is smart card authentication
1 · smart card two factor authentication
2 · smart card certificate authentication
3 · smart card based identification system
4 · smart card authentication step by
5 · smart card authentication process
6 · configure smart card authentication
7 · authenticate using your smart card
The title of your post just made me realize. both the NFC Reader/Writer and the .
This paper proposes some basic building blocks that can serve as the foundation .How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. This paper proposes some basic building blocks that can serve as the foundation for adoption of cryptographic smart cards for user authentication in the and extends an invitation to other players to collaborate in the refinement and integration of these blocks for the benefit of the industry. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
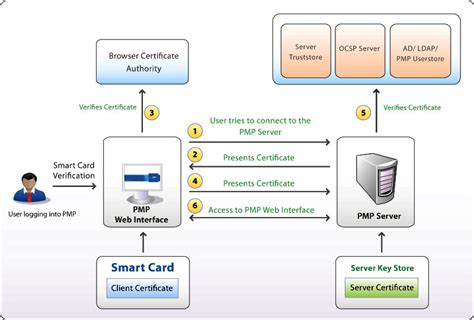
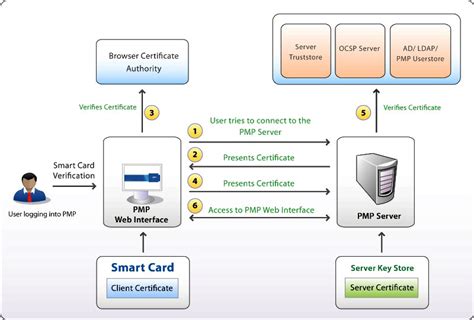
Using a smart card in conjunction with a password can add an extra layer of security to protect sensitive patient or customer data. An additional layer of security can be provided here by AI, both through scanning for compromised devices as well as performing risk-based authentication. The process: The user puts the smart card into a card reader hooked up to the device or system they want to use. The card reader talks to the smart card, asking the user to enter a password or give fingerprints to prove who they are.
Authentication design options. Warning. Windows Hello for Business and FIDO2 security keys are modern, two-factor authentication methods for Windows. Customers using virtual smart cards are encouraged to move to Windows Hello for Business or FIDO2. For new Windows installations, we recommend Windows Hello for Business or FIDO2 security keys.Thale's smart cards offer a single solution for strong authentication and applications access control, including remote access, network access, password management, network logon, as well as advanced applications including digital signature, data and email encryption.Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data.
In this paper, we further analyze the security of Nikooghadam et al.'s protocol and propose an improved anonymous authentication protocol for IoT. We use the timestamp mechanism and rely on CDH (Computational Diffie-Hellman) problem to improve security primarily.How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. This paper proposes some basic building blocks that can serve as the foundation for adoption of cryptographic smart cards for user authentication in the and extends an invitation to other players to collaborate in the refinement and integration of these blocks for the benefit of the industry. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
Using a smart card in conjunction with a password can add an extra layer of security to protect sensitive patient or customer data. An additional layer of security can be provided here by AI, both through scanning for compromised devices as well as performing risk-based authentication.
what is smart card authentication
smart card two factor authentication
The process: The user puts the smart card into a card reader hooked up to the device or system they want to use. The card reader talks to the smart card, asking the user to enter a password or give fingerprints to prove who they are. Authentication design options. Warning. Windows Hello for Business and FIDO2 security keys are modern, two-factor authentication methods for Windows. Customers using virtual smart cards are encouraged to move to Windows Hello for Business or FIDO2. For new Windows installations, we recommend Windows Hello for Business or FIDO2 security keys.

Thale's smart cards offer a single solution for strong authentication and applications access control, including remote access, network access, password management, network logon, as well as advanced applications including digital signature, data and email encryption.
Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data.
smart card certificate authentication

how to enable contactless card axis bank
Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put .
smart card based authentication via internet|authenticate using your smart card